ARM Announces New 28nm POP IP For UMC Foundry
Today ARM announces a new POP IP offering directed at UMC’s new 28HPCU manufacturing process. To date we haven’t had the opportunity to properly explain what ARM’s POP IP actually is and how it enables vendors to achieve better implementation of ARM’s IP offerings. While for today’s pipeline announcement we’ll be just explaining the basics, we’re looking forward to a more in-depth article in the following months as to how vendors take various IPs through the different stages of development.
When we talk about a vendor licensing an ARM IP (CPU for example), this generally means that they are taking the RTL (Register Transfer Level) design of an IP. The RTL is just a logical representation of the functioning of a block, and to get to from this form to one that can be implemented into actual silicon requires different development phases which is generally referred to as the physical implementation part of semiconductor development.
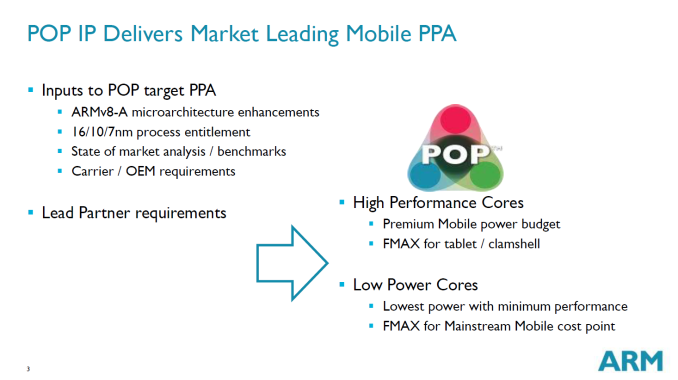
It’s here where ARM’s POP IP (Which by the way is not an acronym) comes into play: Roughly speaking, POP IP is a set of tools and resources that are created by ARM to accelerate and facilitate the implementation part of SoC development. This includes standard cell libraries, memory compilers, timing benchmarks, process optimized design changes and in general implementation knowledge that ARM is able to amass during the IP block development phase.
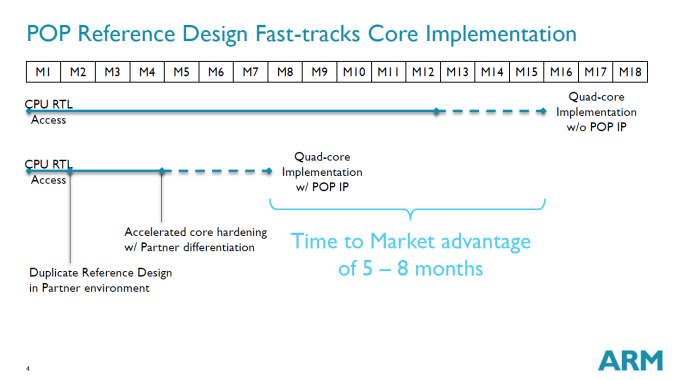
The main goal is to relieve the vendor from re-doing work that ARM has already done and thus enable a much better time-to-market compared to vendors which have their in-house implementation methodology (Samsung and Qualcomm, among others, for example). ARM explains this can give an up to 5-8 month time to market advantage which is critical in the fast-moving mobile SoC space.
One aspect that seemed to be misunderstood, and even myself had some unclear notions about, is that POP IP is not a hard-macro offering but rather all the resources that enable a vendor to achieve that hard-macro (GDSII implementation).
This is where we come back to today’s announcement. ARM’s new POP IP targets UMC’s new 28nm process called 28HPCU for ARM’s Cortex A7 and Cortex A53 cores. The acronym has a dual meaning standing for 28nm High Performance Compact “UMC” or “Ultra-Low IDDQ” with IDDQ being the leakage current which is being describes as being considerably lower than UMC’s first-generation 28nm HKMG process and able to give significant battery life improvements to devices.
While ARM isn’t able to disclose which vendors use POP IP, they state that the main target is low-cost Asian market, which most likely means various Chinese vendors. According to S.C. Chien, vice president, corporate marketing, UMC:
“Multiple customers from a variety of applications have engaged with UMC to design their products on 28HPCU. Our collaboration with long-time partner ARM enables UMC to offer a comprehensive design platform with POP IP for two of the most efficient ARM processor cores.”